Your workforce is using AI. Do you know what they’re doing with it?
Neon Cyber is the AI-native platform built specifically to give security teams complete visibility into every browser-based AI interaction and workflow across their organization.
The scale of the problem — in numbers.
Unauthorized AI Use
54%
organizations enforce and/or monitor for unauthorized AI use
Unsanctioned Apps
98%
of employees are using unsanctioned apps, including Shadow AI/IT
Confidential Information
32%
of employees have entered confidential customer data into AI tools
Free AI Tools
68%
of employees use free AI tools like ChatGPT via personal accounts
A security expert in every browser session
Neon installs as a lightweight browser extension via your existing MDM or GPO. No new hardware, no network reconfiguration, no replacing the browsers your team already uses.
Most organizations achieve full workforce coverage within 48 hours.
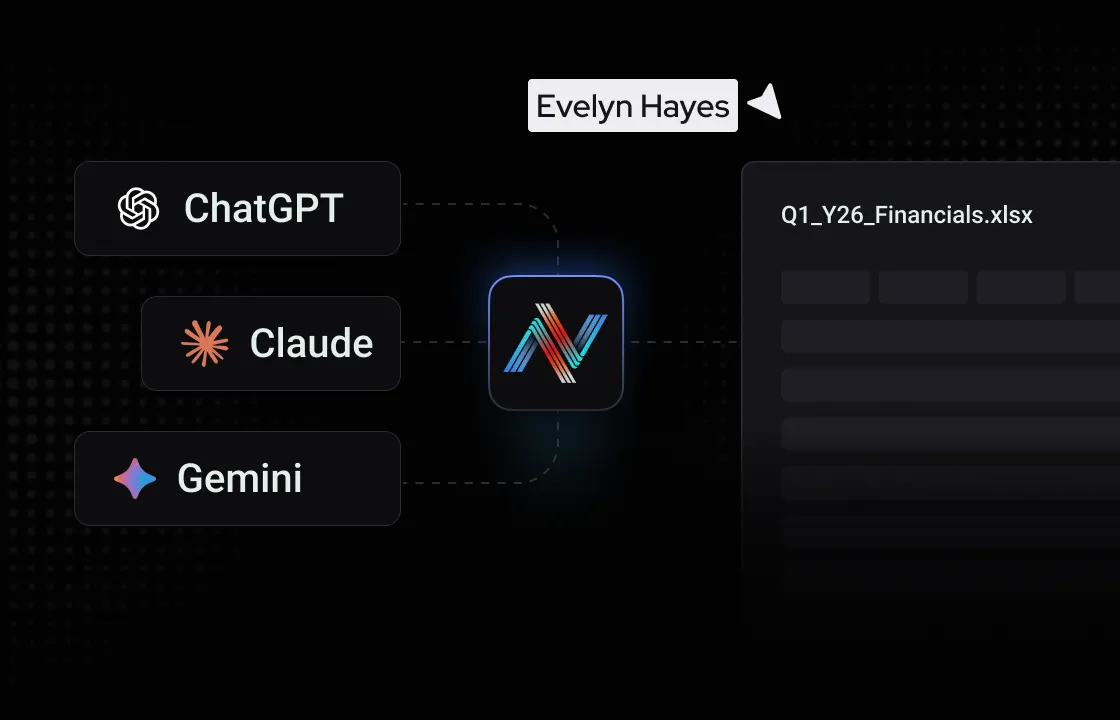
Neon sits with each user in the browser — watching every AI prompt, SaaS login, form submission, and file upload in real time. It captures the who, what, when, and how of browser activity across your organization, including applications that bypass your IDP entirely.
Your IDP has blind spots. Neon doesn't.
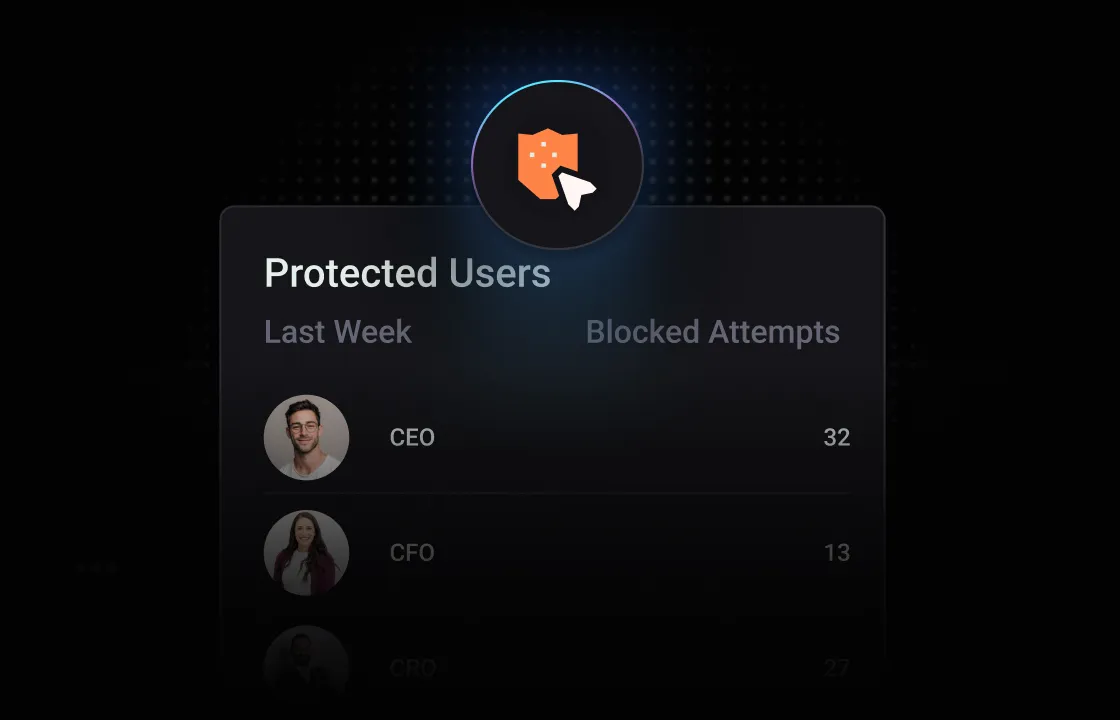
Neon's proprietary Small Language Model (SLM) analyzes intent and context in the moment — flagging AI-powered phishing, data exfiltration, risky authentication behavior, and policy violations before they become incidents.
No waiting for logs. No chasing alerts after the fact.
When a user violates policy — uploading sensitive data to an unsanctioned AI tool, reusing a breached password, or bypassing SSO — Neon delivers a real-time, context-aware warning and captures the event for your security and compliance teams. Automatic. Audit-ready.
Real time, context-aware warnings for security and compliance teams.
When a new policy for a threat is enabled, that policy is propagated to every deployed instance — giving your entire organization herd immunity against emerging campaigns the moment they're identified.
One policy. Every instance. Instant protection.
Everything you need to govern AI in the browser
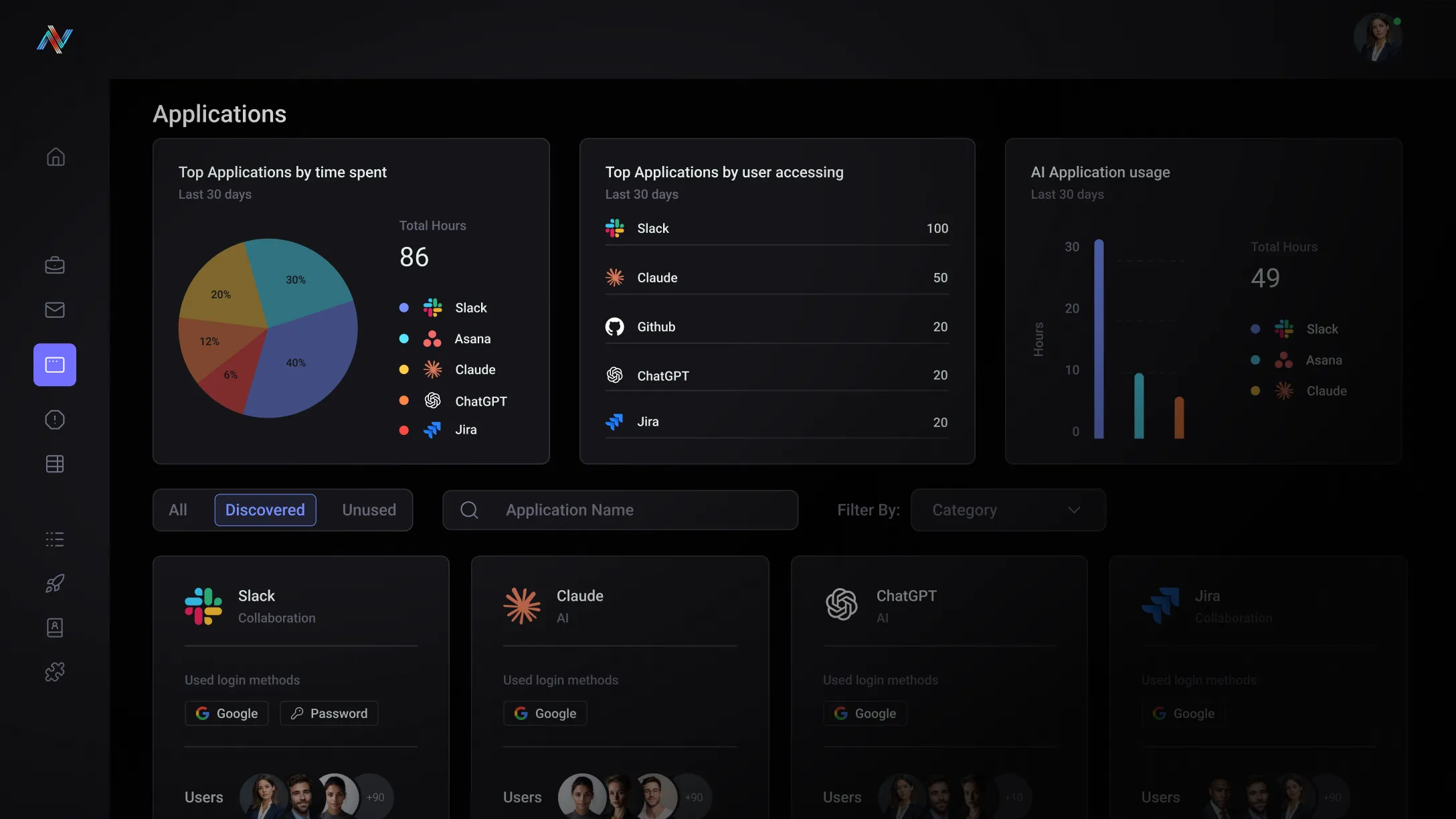
AI & Shadow SaaS Visibility
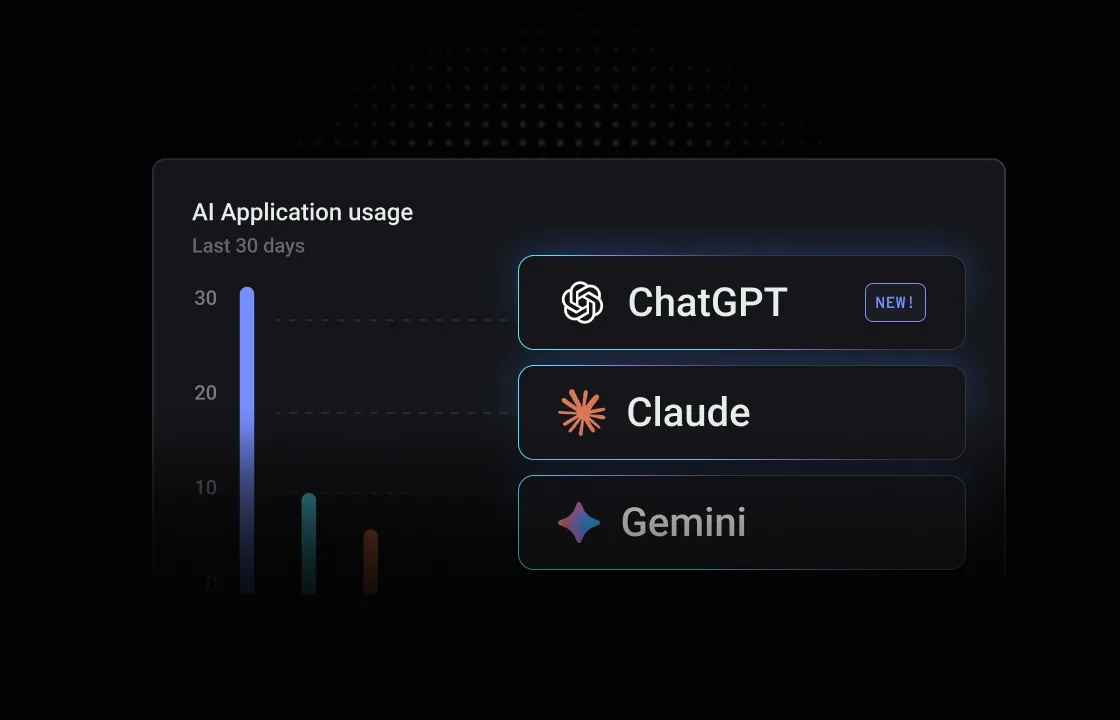
Get a real-time, continuously updated catalog of every AI and SaaS app your users touch — inside your IDP and far beyond it. Know what's being used, by whom, with what data, and whether those vendors meet your data privacy, security, and compliance requirements.
AI Guardrails & Real-Time User Guidance

Replace static blocklists with behavior-based controls that trigger context-aware warnings at the exact moment of risk — guiding users in real time without breaking workflows or killing productivity.
AI-Native Data Leakage & Insider Risk
Monitor every AI prompt, form input, and file upload for data in motion. Neon detects and blocks exfiltration and leakage attempts — whether accidental or intentional — before data can leave via the browser.
AI-Powered Phishing Defense
Neon's SLM analyzes every form, credential field, and page in real time — detecting AI-generated phishing, lookalike domains, and credential harvesting attempts at the point of click, before the user hits submit.
Authentication & Identity Hygiene
Enforce MFA compliance, detect credential reuse and weak passwords, and flag identity-based anomalies with professional and personal accounts — directly in the browser, across every app accessed, sanctioned or not.
Browser Observability for SecOps & GRC

Receive a detailed forensic timeline of browser activity — from input tracking to identity-based anomaly detection — giving SOC teams the full session story they need for threat hunting, incident response, and compliance reporting.
Precision security for the AI era without the friction
See what your stack can't
Complete visibility into browser-based AI and SaaS usage — including shadow apps, unsanctioned tools, and activity that bypasses your IDP entirely.
Stop threats before they land
In-flight detection and blocking at the point of click — not after the fact. No more chasing logs for something that already happened.
Enable AI without enabling risk
Give your organization the freedom to use AI tools without exposing sensitive data, bypassing controls, or creating invisible liability.
Enforce policy where it matters
Real-time, behavior-based controls that enforce governance at the point of decision — not in a policy document nobody reads.

Complement your existing stack
Neon closes the visibility gap your EDR, DLP, and SASE tools leave open the moment a browser tab opens — without replacing what already works.
Deploy fast, see value faster
Enterprise-wide deployment in under 15 minutes via MDM or GPO. Most security teams see their first shadow AI findings within the hour.
One platform, every AI-era use case
Neon's AI-native browser security platform powers six distinct use cases — each addressing a critical gap in how enterprise security teams govern AI adoption, protect sensitive data, and manage browser security risk across their organization.
AI Security
Browser Security
Trusted by security teams who can't afford blind spots
Everything you need to know about Neon Cyber's capabilities and deployment
Neon deploys as a lightweight browser extension and works with all major Chromium-based browsers used in enterprise environments — including Google Chrome, Microsoft Edge, Perplexity's Comet, OpenAI's Atlas, and others. No dedicated or enterprise browser is required. Neon is compatible with Windows and macOS managed devices and can be distributed via MDM, GPO, or direct user installation. Because Neon runs as an extension inside existing browsers rather than replacing them, there is no browser change management required and no risk of it becoming a single point of failure for your environment. Extension updates are handled automatically — no browser restarts, no additional policy pushes, and no IT intervention required when Neon updates.
Yes — this is one of Neon's core use cases. Rather than relying on employee training or retroactive log review, Neon enforces AI acceptable use policies at the exact moment a user interacts with an AI tool in the browser. Security teams can configure behavior-based policies that trigger context-aware interventions in real time — warning a user before they upload a document to an AI tool, or blocking a data submission that violates a defined policy. Policies can be applied by user, role, department, application, or data type, and configured to warn, block, or escalate depending on the sensitivity of the interaction. Every policy trigger event is captured — including user, application, action, and timestamp — giving compliance teams the audit trail needed to demonstrate enforcement. AI tools your organization has sanctioned can operate freely; unsanctioned tools are governed precisely at the point of use. The result is an AI policy that actually runs — not just a document that sits in a shared drive.
Neon is designed to monitor organizational risk — not to surveil individual employees. The platform operates in monitor mode, providing full visibility into security-relevant behaviors without actively capturing or intercepting personal activity. Security teams can define which detections to monitor, what triggers an alert, and what actions are allowed or blocked. What Neon observes is behavioral and contextual: which applications are accessed, what authentication methods are used, whether data is being submitted to risky destinations, and whether data being uploaded to an AI tool like ChatGPT, Gemini, or Claude is allowed. Neon is not designed to capture or store the personal content of general browsing unrelated to security policy. For organizations with employee monitoring disclosure requirements — particularly those operating under GDPR, CCPA, or state-level labor laws — Neon's deployment model supports transparent communication to employees about the scope of monitoring, consistent with your existing acceptable use and IT policies. Enterprise customers are encouraged to work with their legal and HR teams to ensure deployment documentation aligns with applicable privacy regulations and disclosure obligations for their jurisdiction. Neon's team is available to support this process.
Neon captures behavioral telemetry — security-relevant signals about how users interact with applications, forms, credentials, and data in the browser. This telemetry powers real-time detection, policy enforcement, and the forensic timeline available to your security team for threat hunting and incident response. Telemetry data is retained for up to 30 days by default, giving security teams immediate access to recent session history for investigations. Data beyond that threshold can be transferred — reducing cost while preserving the forensic record — or exported directly to your SIEM, allowing you to retain browser telemetry within your own data environment with no dependency on Neon's storage infrastructure. Organizations with strict data residency or retention requirements can configure Neon to minimize on-platform storage entirely by routing telemetry events in real time to their existing SIEM. This is particularly relevant for regulated industries where data sovereignty, retention policy compliance, or third-party data hosting restrictions apply. Neon does not capture or retain the full content of general browsing sessions. Detection is based on behavioral signals and contextual analysis at the point of interaction — not bulk session recording.
It's the right question to ask of any security vendor — and especially one that operates inside the browser. Here's how Neon addresses it directly: No endpoint agent, no proxy, no single point of failure. Neon deploys as a lightweight browser extension, not an endpoint agent or network proxy. This architecture matters because it means Neon cannot become a CrowdStrike-style incident — there is no kernel-level driver, no process that can crash a device, and no network routing dependency that could take down connectivity if something goes wrong. The worst-case scenario of a Neon failure is that the extension stops functioning. Your users keep browsing; your other security tools keep running. No privileged network position. Unlike proxy-based security tools — including many SASE and SSE solutions — Neon does not sit in the network path between your users and the internet. A compromised proxy gives an attacker a man-in-the-middle position across your entire organization's traffic. Neon holds no such position. It operates at the browser session layer only, which fundamentally limits the blast radius if a third-party browser extension were ever targeted. Automatic updates, zero IT burden. Browser extension updates propagate automatically through the browser's native update mechanism — no restart required, no IT intervention, no policy changes needed. This means Neon's own attack surface is continuously patched without creating a lag window that attackers could exploit, which is a known risk with enterprise tools that require manual patching cycles. Extension integrity and supply chain risk. Neon is distributed and managed through enterprise-controlled MDM and GPO channels which eliminates the class of supply chain attacks that target publicly listed extensions. Your IT team controls deployment, versioning, and removal centrally.
Ready to see what’s happening in your browser?