Your identity perimeter ends at SSO. The risk doesn't.
SSO coverage is never 100%. Employees create accounts with personal emails, reuse passwords across tools, and bypass MFA on shadow applications. Neon monitors authentication behavior across every browser session.
Identity and access management was built for sanctioned applications. But when employees can sign up for any SaaS tool in 30 seconds using a personal email, the identity perimeter dissolves. And the risks compound silently.
Shadow identities everywhere
Employees create accounts on AI tools and SaaS apps using personal emails, Google SSO, or social logins that your identity provider never catches. Each one is an unmanaged access point.
Password reuse across boundaries
The same password used for a personal AI tool is used for a corporate app. One breach on either side compromises both. Your credential monitoring only covers the accounts you know about.
MFA gaps on the apps that matter
Your sanctioned apps enforce MFA. The unsanctioned AI tool where someone just uploaded a client list? No MFA, no audit trail, no visibility into who else has access.
Identity hygiene that extends beyond your SSO boundary.
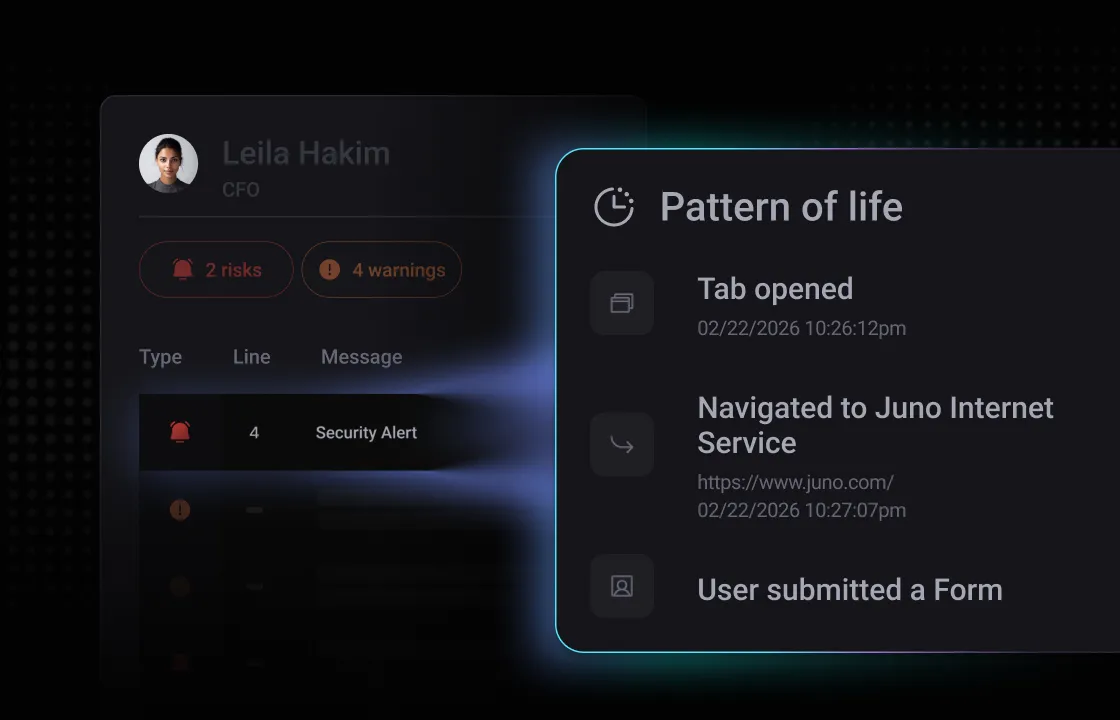
Neon monitors authentication events across every application accessed through the browser — sanctioned or not. Know when accounts are created, how they’re authenticated, and where your identity perimeter is breaking down.
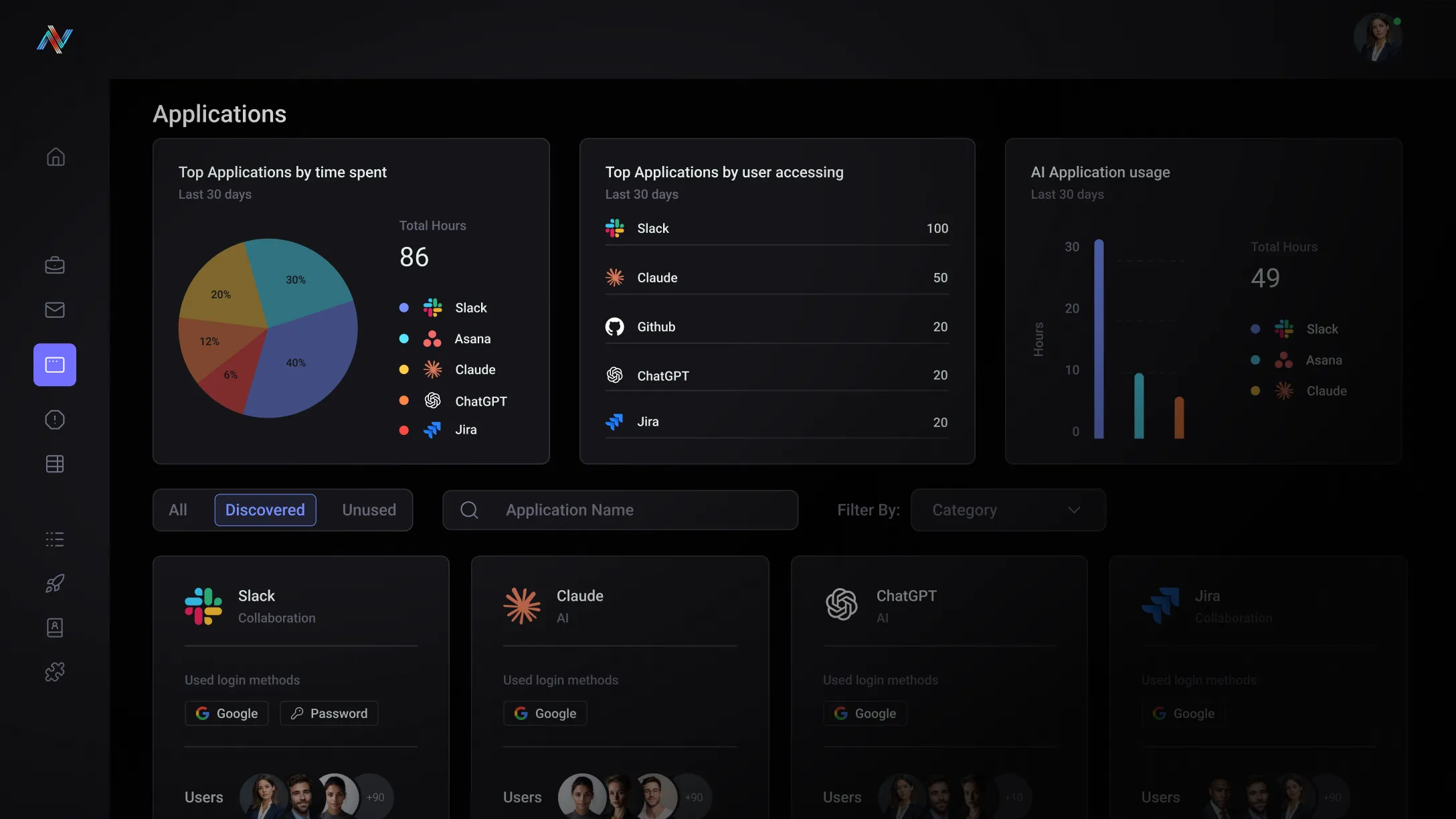
Authentication monitoring
Track every login, signup, and authentication event across all browser-based applications. Flag accounts created outside SSO, weak authentication methods, and MFA gaps.
Identity risk scoring
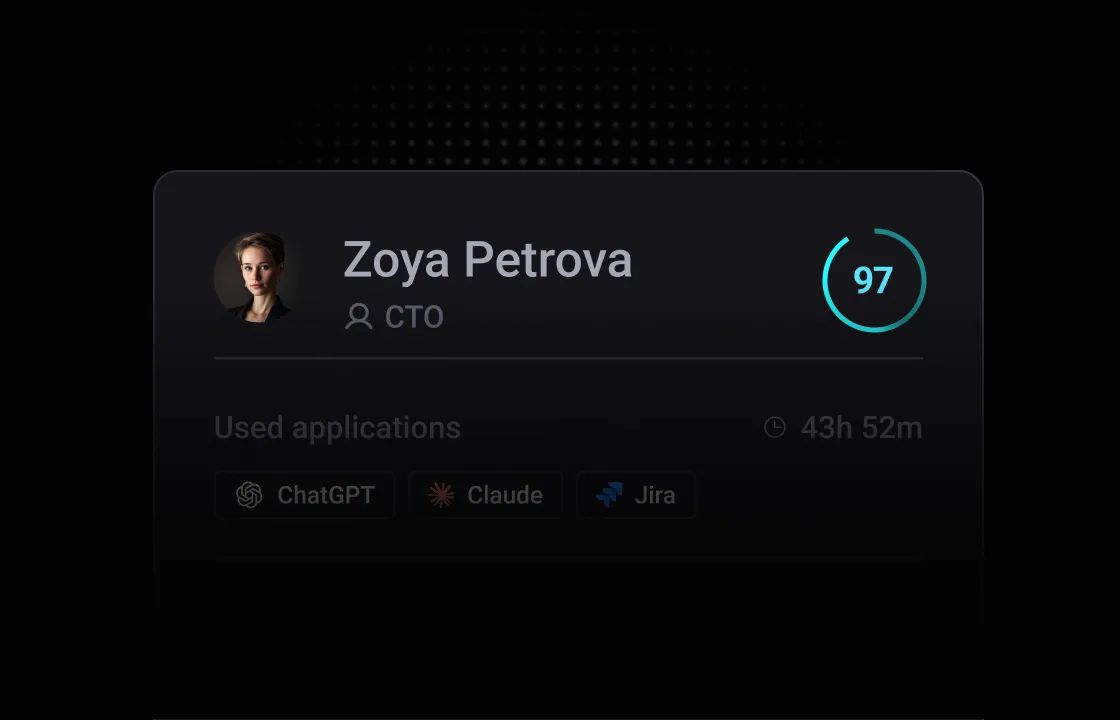
Score users and applications based on authentication hygiene — password reuse indicators, MFA adoption, and the gap between sanctioned and unsanctioned identity usage.
Credential protection
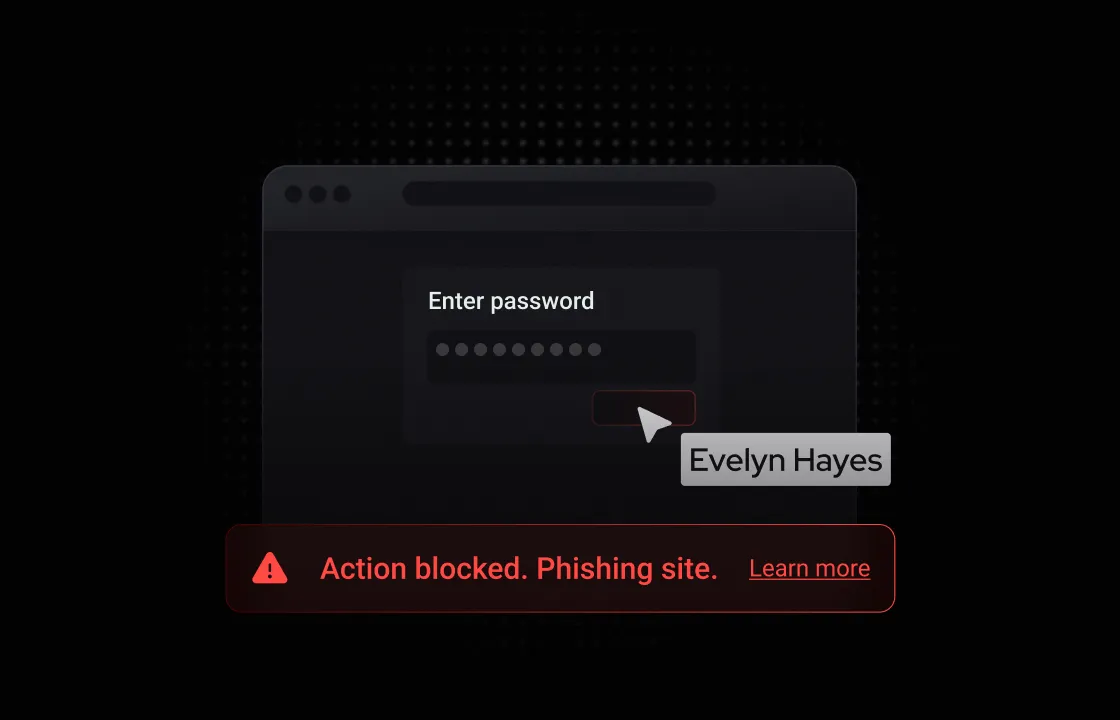
Detect and prevent credential submission to untrusted or malicious sites. Stop password reuse across corporate and personal boundaries before it becomes a breach vector.
Built for your team
The Identity Blind Spot
Your IAM platform governs the accounts you provisioned. It has no visibility into the 40+ shadow accounts each employee quietly creates. Every one of those is an unmonitored credential that could be your next breach entry point.
The Perimeter That Isn't
You've invested heavily in SSO, MFA, and PAM. But your identity perimeter only covers what you know about. The accounts created outside your IdP — using personal emails, social login, and free-tier AI tools — are entirely outside your governance model.
Unlock the potential with Neon Cyber
Monitor authentication events for every browser-based app — including the shadow tools that bypass SSO entirely and never appear in your identity provider logs.
Authentication hygiene is monitored in real time across every session — not surfaced in a quarterly access review that's already months out of date.
Stop credentials from being submitted to phishing sites or reused across personal and corporate boundaries before the breach happens — not after.
Every identity risk finding is scored, attributed, and logged — giving you the evidence trail you need for access reviews, audits, and incident investigations.
Trusted by the best
Everything you need to know about Neon Cyber's capabilities and deployment
Your SSO and IDP only see what flows through them. The moment an employee signs up for a SaaS tool with their corporate email directly on the vendor's login page, creates a free-tier account that never touches your identity provider, or accesses a web application that doesn't support SSO at all — that authentication event is invisible to every identity-layer tool in your stack.
Neon monitors authentication events at the browser layer, which means it sees every login regardless of whether SSO was involved. When a user authenticates to any application in the browser — through your IDP, directly on a vendor login page, or through a personal account — Neon captures the event: the application, the authentication method used, the identity type, and whether the login meets your policy requirements such as MFA enforcement.
This gives security teams a complete picture of authentication behavior across the organization — not just the subset that flows through managed identity infrastructure.
No — and it shouldn't. IAM and PAM platforms are foundational to how organizations manage identity at scale: provisioning and deprovisioning access, enforcing role-based permissions, governing privileged accounts, and maintaining the authoritative record of who has access to what.
What Neon addresses is the enforcement gap that exists between what your IAM and PAM platforms govern and what actually happens when employees open a browser. IAM governs managed identities across managed applications. It has no visibility into how employees authenticate to applications that sit outside that managed perimeter.
Neon sits in that gap. It doesn't replace the identity governance your IAM and PAM platforms provide — it extends enforcement to the layer where that governance ends. The two work together: IAM governs the managed perimeter; Neon governs everything that happens in the browser beyond it.
Yes — and this is one of the most common scenarios Neon surfaces that organizations have no existing visibility into.
The pattern is straightforward: an employee discovers an AI tool, signs up directly with the vendor using their corporate email address. The tool never gets connected to SSO. From your identity infrastructure's perspective, it doesn't exist. From Neon's perspective, it's fully visible.
Because Neon monitors all browser-based authentication events — not just those that flow through managed identity channels — it captures the login, identifies the application, records the authentication method used, and flags whether that access pattern violates your policies.
Organizations running Neon consistently discover AI tools and SaaS applications being accessed with corporate credentials that their IDP has never catalogued — often in the hundreds. Each represents an unsanctioned data handling relationship, a potential compliance exposure, and an identity that can't be deprovisioned through your standard offboarding process because IT doesn't know it exists.
Password reuse between personal and corporate accounts is one of the most common and underappreciated identity risks organizations face.
Neon operates at the browser layer where both types of authentication happen. Because it monitors credential interactions across all browser-based logins on a managed device — not just those flowing through corporate SSO — it can identify when the same credential pattern appears in both a corporate authentication context and a personal account context when used in a browser.
When that signal is detected, Neon flags it as a policy risk and can trigger a real-time warning to the user, an alert to the security team, or both.
A corporate password that's been reused on a personal account is a credential that's exposed to every breach, info-stealer, and credential stuffing campaign that targets consumer platforms. By surfacing that reuse in real time, Neon gives security teams the opportunity to intervene before a compromised personal credential becomes a corporate incident.
It's one of the most deliberate and hardest-to-detect workarounds in the shadow AI problem — and the risk is considerably higher than most organizations account for.
When an employee uses a personal account to access an AI tool on a corporate device, they're bypassing every data governance control your organization has built around corporate identity. Data entered into a personal ChatGPT account or a personal Gemini session is governed entirely by that platform's terms of service — not your data handling policies. It can't be deprovisioned when the employee leaves.
The motivation is often entirely benign — employees use personal accounts to access apps they need, to use features their corporate subscription doesn't include, or simply because the personal account is already open. The intent doesn't change the risk.
Neon addresses this by operating at the browser layer, where it can differentiate between enterprise identity and personal identity within the same browser session. The result is governance that applies at the point of data entry — not at the identity layer, where personal accounts are invisible by design.
Every identity. Every authentication. Every app. Governed.