You can't govern what you don't know exists. Neon finds all of it.
Your workforce is using AI tools and SaaS apps you've never approved, never audited, and never even heard of. Neon discovers all of it — in real time, across every browser.
Shadow AI and SaaS sprawl are growing faster than any manual audit can track. Traditional discovery relies on network logs and SSO integrations — but the riskiest tools are the ones that bypass both entirely.
Invisible adoption
Employees sign up for AI tools with personal emails, bypassing SSO entirely. Your identity provider never sees it. Your CASB never flags it. But sensitive data is already flowing.
No context, just noise
Network logs tell you a domain was visited. They don’t tell you what was typed into the prompt, what was uploaded, or whether it violated policy. You’re counting hits, not assessing risk.
Sprawl compounds weekly
Every department finds their own AI tool. Marketing uses one. Engineering uses three. Legal uses another. By the time IT audits the list, it’s already out of date.
Complete AI and SaaS discovery from the browser out.
Neon monitors all browser-based activity to build a living inventory of every application your workforce touches — sanctioned or not. No network tap required. No SSO dependency. Just truth.
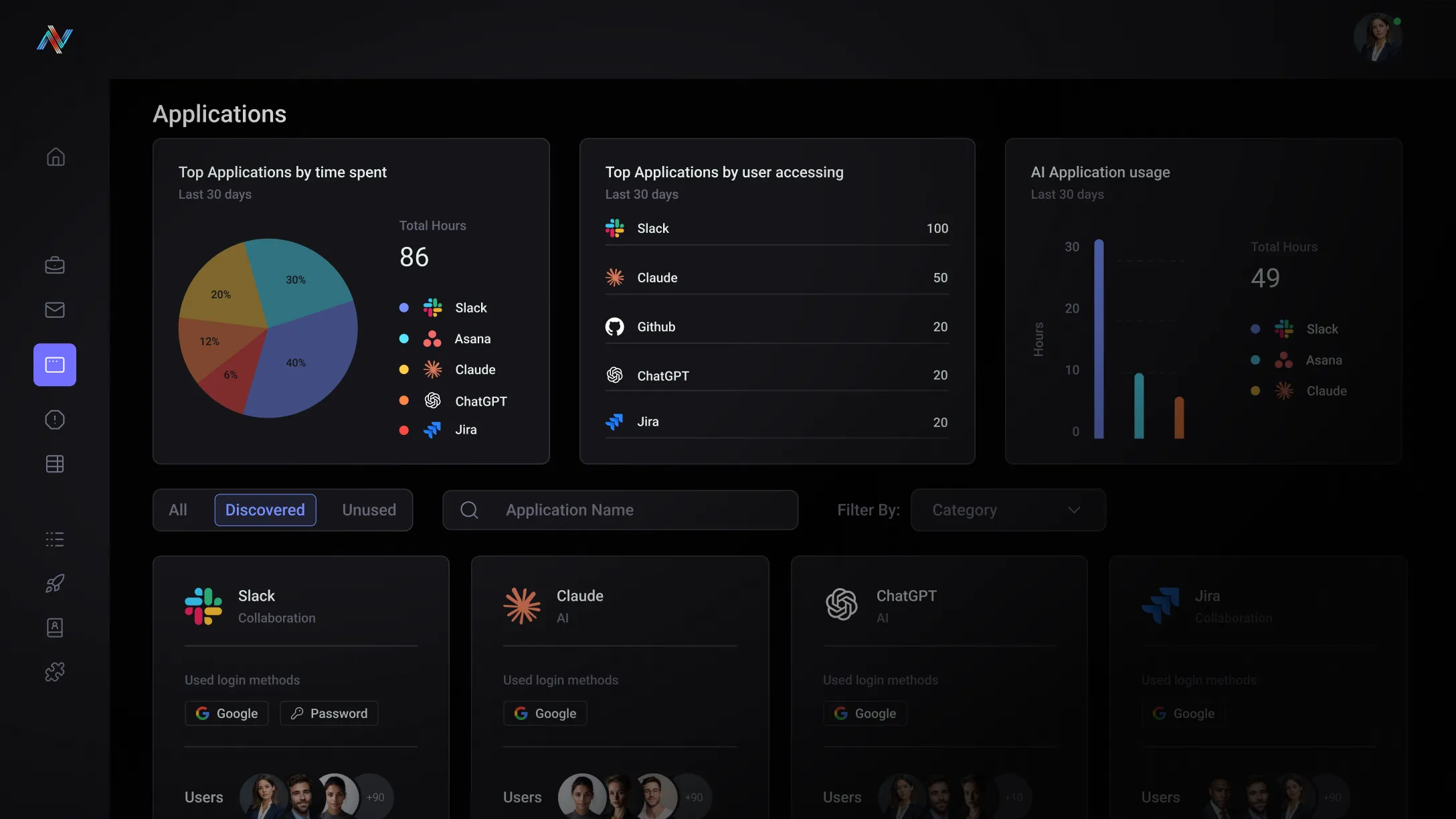
Application inventory
Every SaaS app and AI tool accessed by your workforce, automatically cataloged with vendor compliance data, data-sharing practices, and authentication capabilities.
Identity mapping
See which accounts were created outside SSO, which users have multiple identities across tools, and where authentication hygiene is breaking down.
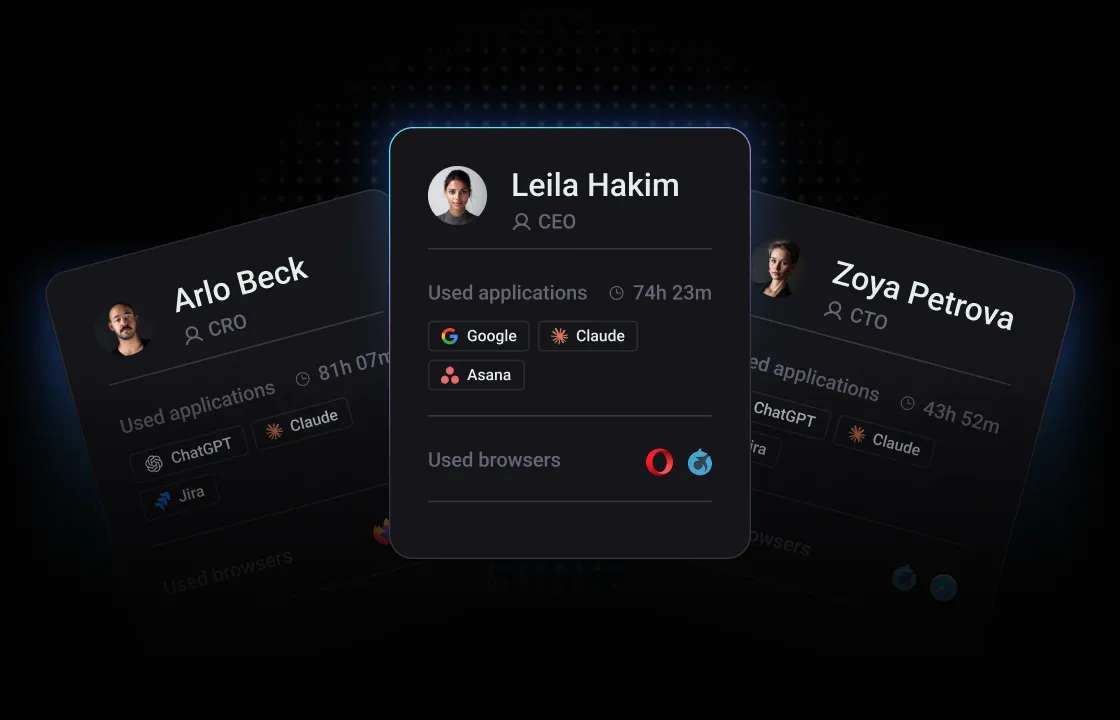
Usage intelligence
Understand adoption trends, data flow patterns, and risk concentration. Know not just what tools are in use — but how they’re being used and with what data.
Built for your team
The Visibility Gap
You're responsible for governing AI usage but your current stack gives you zero browser-layer telemetry. Network logs show a domain. They don't show a prompt. You're defending against a threat you can't see.
The Compliance Risk
Shadow SaaS creates audit exposure that surfaces during SOC 2 and ISO 27001 reviews. You need a living inventory — not a quarterly spreadsheet that's out of date before it's finished.
Unlock the potential with Neon Cyber
Neon illuminates every AI tool and SaaS app your team touches — including accounts created entirely outside your identity provider.
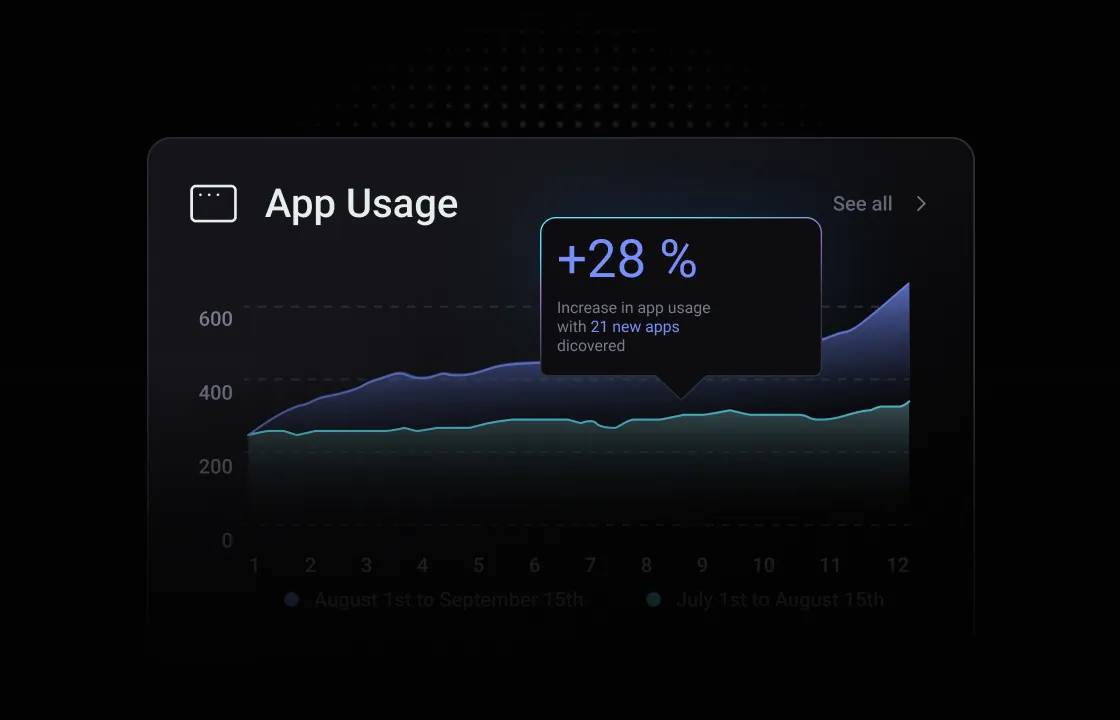
Your app inventory updates continuously as new tools are adopted — not quarterly when an audit forces the exercise.
Every discovered app is automatically scored on compliance posture, data-sharing practices, and authentication capabilities.
Works inside the browsers your team already uses. No proxy rules, no network tap, no hardware. Enterprise-wide in under 15 minutes.
Trusted by the best
Everything you need to know about Neon Cyber's capabilities and deployment
Your identity provider is only as comprehensive as the applications employees log into through it. The moment a user signs up for an AI or SaaS tool with their personal email, creates a free-tier account outside your SSO flow, or accesses a web-based application that doesn't require authentication at all — your IDP goes dark. It never sees it, never logs it, and never flags it.
That's the gap Neon's AI & SaaS Application Catalog is built to close.
Neon monitors all browser-based application activity directly — independent of how a user authenticated, whether SSO was involved, and whether your IT team has ever heard of the application. Every AI tool, SaaS platform, and web-based service accessed through the browser is captured in real time, giving security teams a live inventory that reflects what's actually in use across the organization, not just what IT sanctioned.
For each application in the catalog, Neon surfaces:
- Who is using it — individual users, departments, and usage frequency
- How they're accessing it — corporate SSO, personal credentials, or no authentication at all
- What the vendor's security posture looks like — compliance certifications (SOC 2, HIPAA, ISO 27001), data-sharing practices, and data handling policies, continuously audited by Neon's AI model
Your IDP only manages the apps you know about. Neon's AI & SaaS Application Catalog tells you which apps your users actually use. In most environments, those two lists look very different — and the gap between them is where shadow AI and shadow SaaS risk lives.
Neon supports both managed and unmanaged device environments. For BYOD and contractor scenarios, Neon can be deployed via IDP integration — allowing organizations to enforce policies on devices that fall outside MDM or GPO management without requiring hardware enrollment.
Because Neon is OS-agnostic and operates as a browser extension rather than an endpoint agent, it imposes no footprint on the underlying operating system of an unmanaged device. Users on BYOD or contractor devices can be onboarded by distributing the extension directly via email or through your IDP.
This makes Neon particularly effective for organizations with large contractor populations, distributed remote teams, or hybrid environments where full endpoint management is not practical — delivering the same visibility and enforcement capabilities regardless of how or where a device is managed.
Most organizations have written an AI acceptable use policy. Very few have a way to enforce it. Neon bridges that gap in four concrete ways:
Visibility: Neon gives you a real-time inventory of every AI tool being accessed across your organization — sanctioned and unsanctioned — so you understand the scope of what you're governing before you try to govern it.
Real-time enforcement: Policy rules are applied at the point of interaction, not after the fact. Users receive context-aware guidance in the moment, which drives behavior change more effectively than retroactive notification or periodic training.
Audit evidence: Every policy trigger is captured as a structured event — user, application, action, data classification, and outcome — giving your GRC team the audit trail needed to demonstrate policy compliance to auditors, regulators, or the board.
Policy iteration: Because Neon surfaces exactly where and how your policy is being tested in practice, your security team can refine rules based on real behavior data — not assumptions about how employees use AI.
For organizations still developing their AI policy, Neon's SaaS Application Catalog provides the baseline visibility needed to make that policy grounded in reality — showing which tools are already in use, how they're being used, and if data is moving through them.
Stop discovering shadow AI after the damage is done.