AI made phishing smarter. Your defense needs to be smarter too.
AI-generated phishing is personalized, grammatically flawless, and nearly indistinguishable from legitimate communications. Static blocklists and domain reputation checks can't keep up. Neon analyzes intent in real time.
Phishing and social engineering attacks have fundamentally changed. Attackers use AI to generate convincing lures at scale, create pixel-perfect spoofs, and adapt messaging in real time. They're using real infrastructure and multiple hops to mask a URL's final destination. The browser is where these attacks land — and where they need to be stopped.
AI-generated attacks at scale
Attackers use LLMs to craft personalized phishing at a volume and quality that was impossible two years ago. Every email, every fake login page, every social engineering attempt is tailored and convincing.
Blocklists are always behind
By the time a malicious domain hits a blocklist, thousands of users have already been exposed. Attackers spin up and burn through domains faster than any reputation system can catalog.
The attack surface is the browser
Phishing doesn't stop at the email. It lands in the browser — fake login pages, credential harvesting forms, malicious OAuth prompts. Your email gateway can't protect what happens after the click.
A security expert in every browser session.
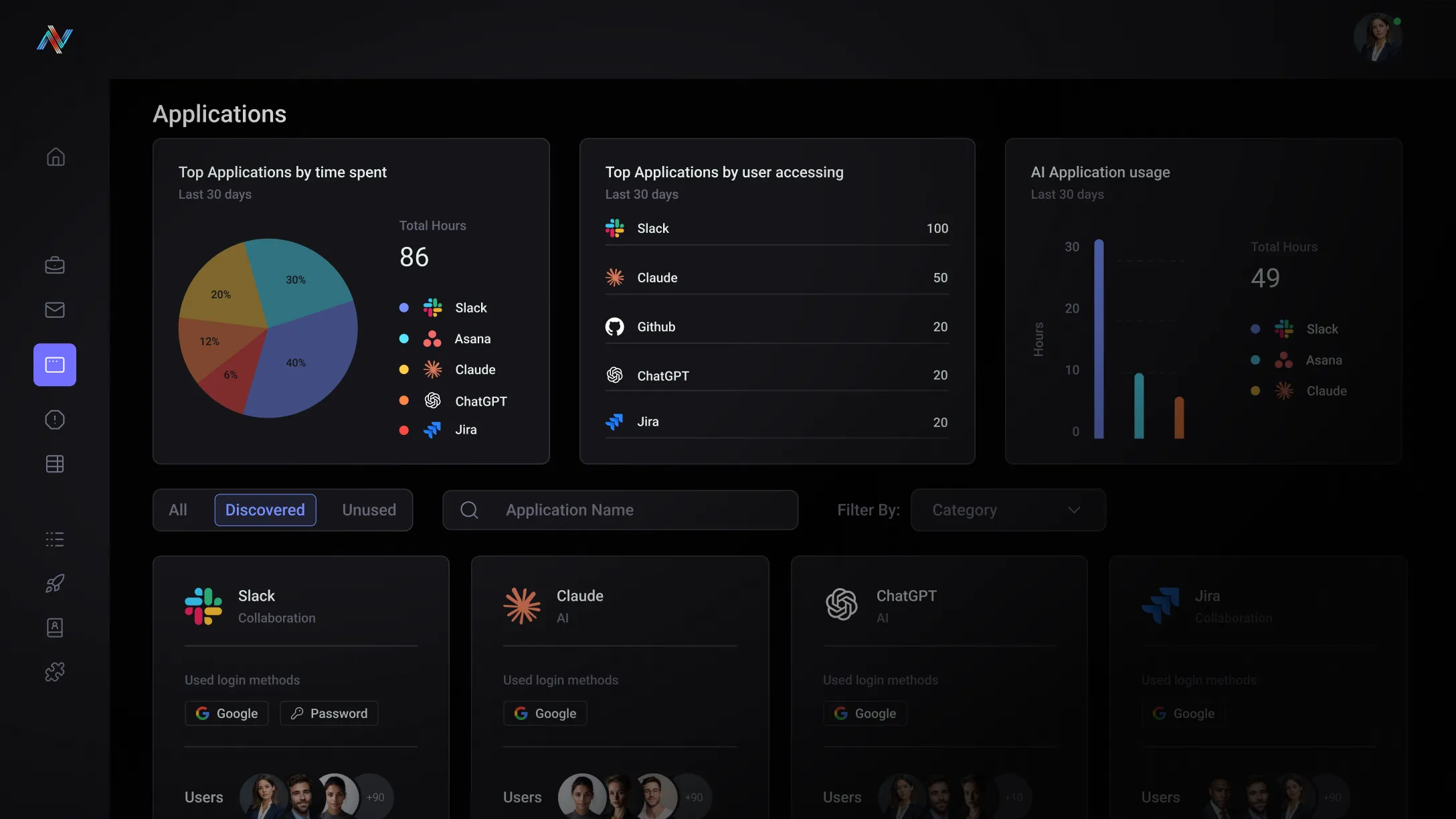
Neon monitors every form, field, and interaction on every website in real time. Its SLM analyzes page content, form behavior, and submission targets to detect phishing and social engineering as it happens — not after.
Real-time page analysis
Neon evaluates every page your workforce visits — analyzing expected destinations, forms, login fields, and submission endpoints for phishing indicators that static lists can't catch.
Enterprise herd immunity
When Neon detects a new phishing campaign targeting one user, policies propagate across your entire workforce. One policy can stop the whole campaign.
Zero-delay blocking
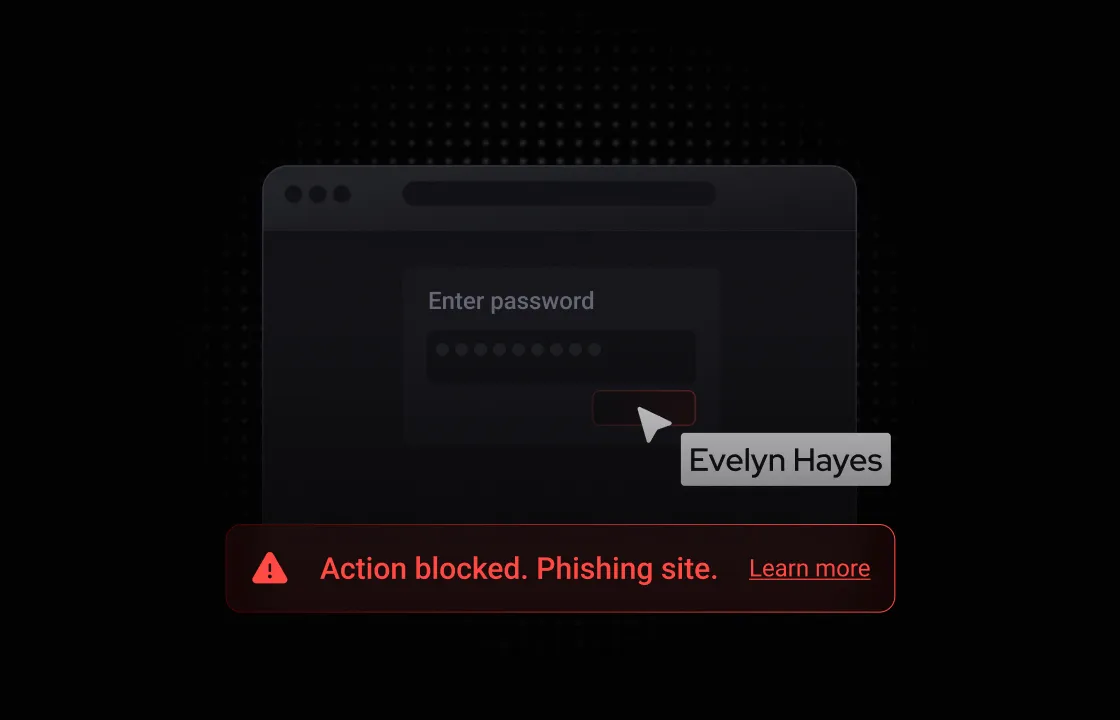
Block malicious form submissions and credential harvesting before the user clicks submit. The attack is stopped in-flight — no post-incident remediation needed.
Built for your team
The Post-Click Gap
Your email gateway catches threats before the click. But once a user lands on a phishing page, you're blind. The credential harvesting form, the fake OAuth prompt, the pixel-perfect spoof — all of it happens in the browser, outside the reach of every tool you have except Neon.
The Domain Rotation Problem
You maintain blocklists but attackers burn through new domains faster than you can add them. Every campaign starts with a clean domain that reputation systems have never seen. You need detection based on behavior and intent — not domain age.
Unlock the potential with Neon Cyber
Your email gateway covers pre-click. Neon covers what happens after — inside the browser where credential harvesting and social engineering actually execute.
Detection is based on page behavior and intent — not domain age or reputation scores. Zero-day phishing domains are caught on the first encounter, not the hundredth.
When any employee encounters a new phishing campaign, policies and protection can propagate to every covered device easily. Your whole organization benefits from every individual detection.
Credentials are blocked before submission. There's no breach to remediate, no password reset campaign to run, no incident report to write.
Trusted by the best
Everything you need to know about Neon Cyber's capabilities and deployment
Phishing has changed fundamentally. A decade ago, attacks were detectable by their telltale signs — suspicious sender addresses, obvious malicious domains, broken grammar, and generic lures. Today's attacks share none of those characteristics. They're AI-generated, native English, highly personalized, and increasingly built on legitimate infrastructure.
The attack no longer lives in the email. It lives in the browser — on the page the user lands on after they click.
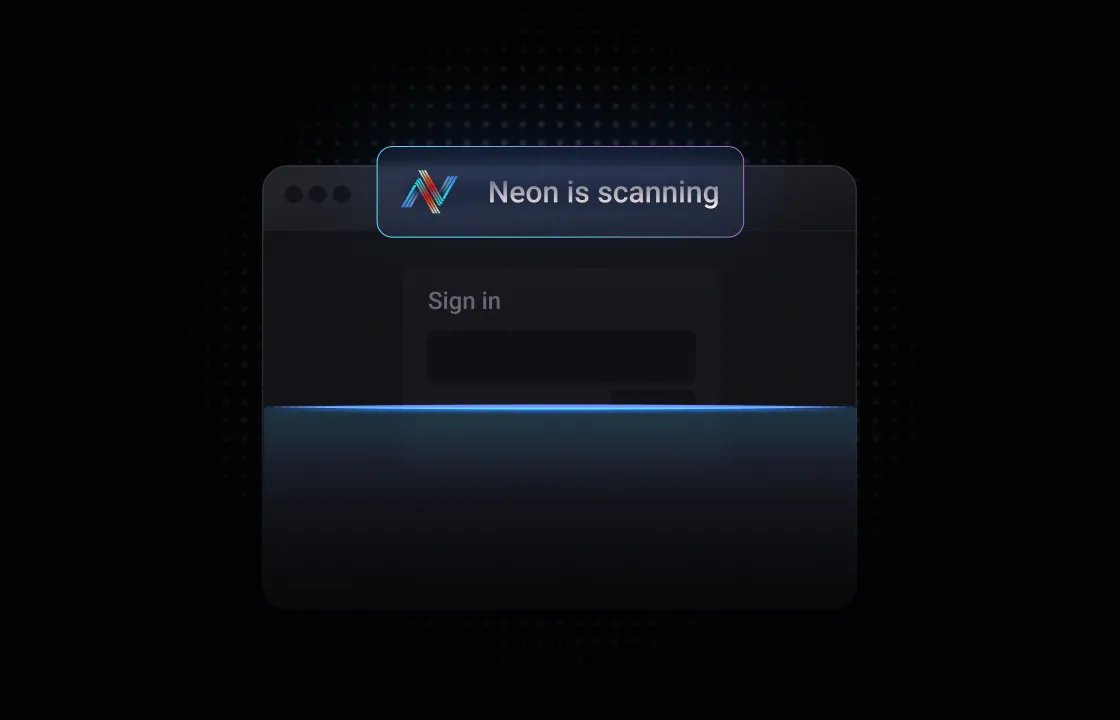
Neon is built for this reality. Rather than analyzing the email or the domain, Neon's protection activates the moment a user clicks on a page and begins to interact with it. Neon's SLM monitors URL destinations, form fields, credential inputs, and data submissions in real time — analyzing both the content of the page and the behavioral context of the interaction to determine whether what's happening in the browser is a phishing attack in progress.
When it is, Neon blocks the submission before credentials or sensitive data are captured, and can propagate corresponding policies across every other deployed instance in the organization.
The result is defense at the point of click — where attacks actually complete — rather than earlier in the chain where today's most sophisticated campaigns have already learned to evade detection.
Signature-based detection works by maintaining a database of known threats — specific domains, IP addresses, URLs, file hashes, and patterns that have been previously identified as malicious. When a user encounters something that matches a known signature, it's blocked. When they encounter something that doesn't match — a brand new phishing domain, a legitimate site being abused — it passes through undetected.
The fundamental limitation of signature-based detection is that it can only catch what it already knows.
Neon's SLM takes a categorically different approach. Rather than matching against a database of known bad, it analyzes what's actually happening in the browser — the structure and intent of the page, the behavior of its form fields, the context of the user's interaction, and the full sequence of events. It doesn't need to have seen a specific attack before to recognize that an interaction is malicious. It understands intent.
This matters because AI has dramatically lowered the cost and complexity of generating novel phishing content. Attackers can now spin up convincing, unique credential harvesting pages in minutes — fast enough to stay permanently ahead of any signature database. Neon's SLM doesn't need to keep up with that volume because it isn't chasing signatures. It's reading behavior.
Email security tools and DNS filtering were built for a different threat model — and that model no longer describes how most phishing attacks work.
Email security tools analyze the message: sender reputation, domain age, links, and attachment types. But modern phishing campaigns are designed to pass that inspection. Attackers send from legitimate infrastructure — a real SharePoint tenant, a real DocuSign account — because those domains have sterling reputations and email security has no basis to block them.
DNS filtering has the same structural limitation. It blocks connections to known malicious domains — but it evaluates the domain name, not what's on the page. A phishing site hosted on a freshly registered domain passes through. So does an attacker-in-the-middle campaign that proxies a legitimate site.
Neon's analysis goes beyond this. It analyzes the link in an email but also compares that to its expected destination and what happens when the user gets there — all of this is inside the browser session, at the point of interaction. That's not a gap that email security or DNS filtering can close by iterating on what they already do. It requires a fundamentally different point of presence in the security stack.
Reputation-based detection has a zero-day problem: every phishing page is new at some point. Attackers know this and exploit it deliberately. By the time a phishing domain is flagged, catalogued, and distributed to blocklists, the campaign it was built for has often already run.
Neon doesn't rely on reputation. Its SLM evaluates what a page is doing, not what its domain has done before. When a user lands on a page — regardless of domain age or reputation — Neon analyzes the page's structure, the behavior of its forms and input fields, the presence of credential capture mechanisms, and the full pattern-of-life context.
A convincing fake login page for a corporate identity provider looks suspicious to Neon not because the domain is flagged, but because of how the page is constructed and how it behaves when a user interacts with it.
In both cases, Neon's detection is grounded in real-time behavioral analysis rather than historical reputation, which means a page being new offers attackers no protective advantage.
Propagation of policies are effectively instantaneous. When Neon detects a confirmed threat on one user's device — a new phishing campaign, a credential harvesting page, a malicious pattern previously unseen — a policy can easily be turned on to block the site or data inputs on that site, and that protection is pushed to every other deployed instance across the organization in real time.
The next employee who encounters the same attack is protected before they interact with it, regardless of geography.
This is what Neon's herd immunity model means in practice. In a traditional security model, the first user to encounter a novel threat is the most exposed — their interaction generates the detection data that eventually protects everyone else, after a lag that can span hours or days.
Neon collapses that window. Protection for user one becomes the protection for users two through ten thousand, immediately.
Stop phishing where it actually happens - in the browser.